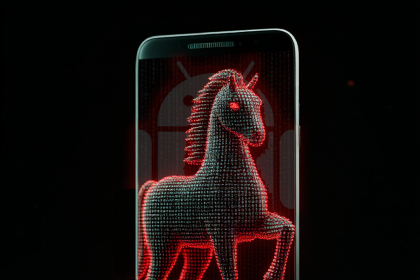
A new malicious campaign named EtherRAT is actively targeting enterprise administrators using a combination of search engine manipulation and fake GitHub pages. Researchers have uncovered this operation which distributes a remote access trojan through what appears to be legitimate software download sites. The attackers are poisoning search engine results to trick IT professionals into visiting fraudulent pages that mimic popular development tools.
The Attack Method
The campaign relies heavily on creating fake GitHub repositories and project pages that look authentic. When an enterprise admin searches for specific software tools, the poisoned results lead them to these cloned websites. Once visitors attempt to download the software, they instead receive the EtherRAT payload. This technique exploits the trust that technical users place in GitHub as a reliable source for tools and code.
SEO Poisoning Tactics
EtherRAT gives attackers full remote control over infected systems, allowing them to steal credentials, exfiltrate sensitive data, and move laterally within corporate networks. The malware is particularly dangerous in enterprise environments where administrators have elevated system privileges. The campaign appears to focus on tools commonly used by DevOps and IT operations teams.
EtherRAT’s Capabilities
Organizations should verify the authenticity of any software downloaded from GitHub or external repositories. Security teams are advised to review their search engine usage policies and consider blocking access to non approved download sources. No specific CVEs are associated with this campaign at this time, as it relies on social engineering rather than exploiting specific code vulnerabilities.
Source: EtherRAT Campaign Uses SEO Poisoning and GitHub Facades to Target Enterprise Admins