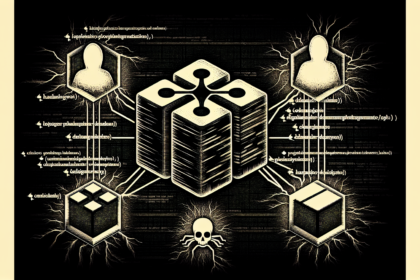
The attack uses malicious proxy servers that sit between the user and legitimate login pages to steal both credentials and session cookies.
Attack Mechanism
Attackers are deploying advanced adversary in the middle (AiTM) phishing pages to intercept login credentials and session cookies for major cloud services. These AiTM kits act as a proxy between the victim and legitimate sites like SharePoint, HubSpot, and Google Workspace, capturing both the username and password and the authentication token. This allows the attacker to bypass multifactor authentication (MFA) protections.
Impact and Scope
The campaign targets business users across multiple industries, with the stolen session cookies enabling persistent access to corporate email, file storage, and customer relationship management tools. Once inside, attackers can perform lateral movement, data exfiltration, and business email compromise. No specific CVEs were cited for this attack, as it exploits standard web authentication protocols rather than a software vulnerability.
Source: Cyber Security News