How It Works
Microsoft researchers have demonstrated that large language models can produce realistic command lines and process trees that mimic human operated intrusions. The system learns from curated telemetry data and red team exercises to propose coherent sequences of commands. It considers argument order, common administrative patterns, and how commands naturally chain together during actions like lateral movement or credential theft.
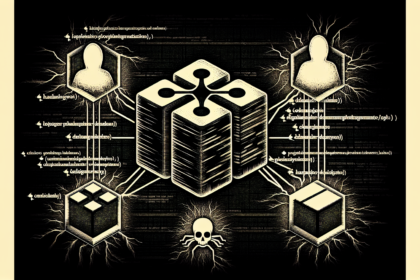
The approach uses a three stage AI agent pipeline that prompts for attack scenarios and iteratively refines the output. This allows the generation of synthetic attack telemetry that looks and behaves like real malicious activity, without exposing production systems to actual malware.
Impact and Scope
This development enables security teams to flood their environments with convincing synthetic attacks for stress testing detection logic at scale. Traditional testing relies on limited scripts or replayed incidents that rarely capture the creativity of modern threat actors. AI generated telemetry offers a repeatable way to evaluate analytics before real attackers appear in logs.
Teams can also use these synthetic scenarios to train analysts, tune triage workflows, and understand how logging changes affect visibility over time. The generated commands are executable in lab environments, providing a safe method to validate defenses against diverse and realistic threats.
Source: Cyber Security News