The Attack Chain
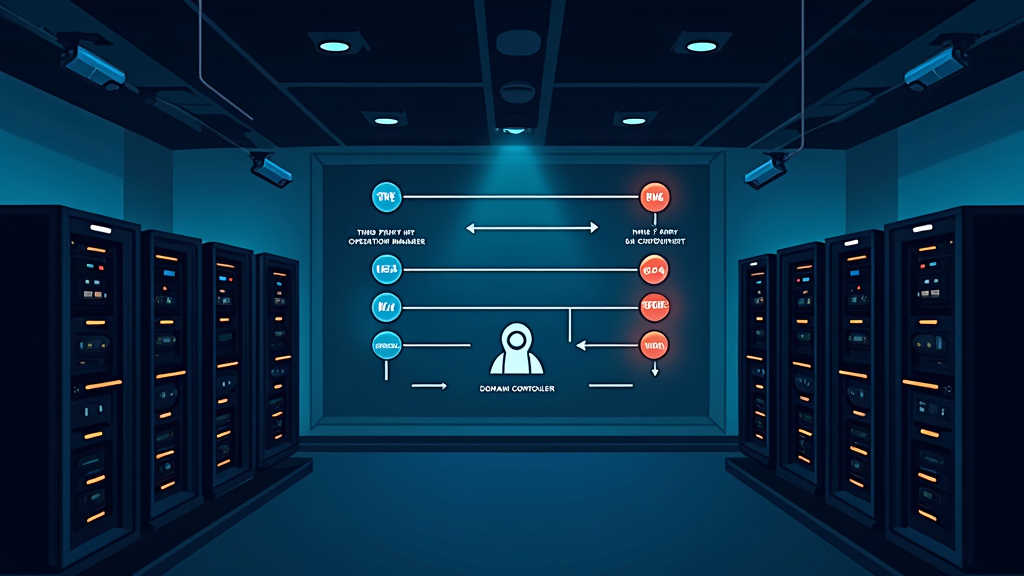
Researchers at Microsoft’s Incident Response team uncovered a sophisticated intrusion campaign that weaponized a trusted enterprise management tool. The attackers compromised a third-party IT services provider to gain initial access, then moved laterally through the victim’s network using only legitimate, pre-approved software. No malware was deployed at any stage, allowing the activity to evade detection systems.
The primary delivery mechanism was the HPE Operations Agent (OA), a widely used monitoring tool. The attackers exploited the trust placed in this software because it already had legitimate access across the target environment. Microsoft confirmed that no vulnerability in HPE OA was involved. The tool was simply co-opted as a delivery channel since its activity blended in with routine administrative operations.
Campaign Duration and Tactics
The intrusion spanned over 100 days from initial compromise to incident response engagement. During this period, the attackers harvested credentials, moved laterally across sensitive systems including domain controllers and SQL servers, and established covert tunnels using ngrok to maintain persistent access. All malicious activity flowed through the trusted HPE Operations Manager (HPOM) management channel, which was managed by the compromised third-party IT provider.
The attackers pushed VBScripts, particularly a file named abc003.vbs, to multiple servers including web servers and domain controllers. These scripts quietly gathered system information, mapped the network, and performed Active Directory discovery. Because the scripts ran through an approved and signed management platform, security tools did not flag the activity.
Broader Implications
This campaign represents a significant shift in attacker methodology. Sophisticated threat actors are increasingly measured not by the complexity of their malware, but by their ability to disappear inside trusted environments and remain undetected for extended periods. By weaponizing tools that organizations already trust and allow, attackers can bypass traditional security controls that focus on blocking malicious files or known bad behaviors. Organizations must now consider how to detect abuse of legitimate management tools, which requires monitoring for anomalous behavior patterns rather than signature based detection.
Source: Cyber Security News