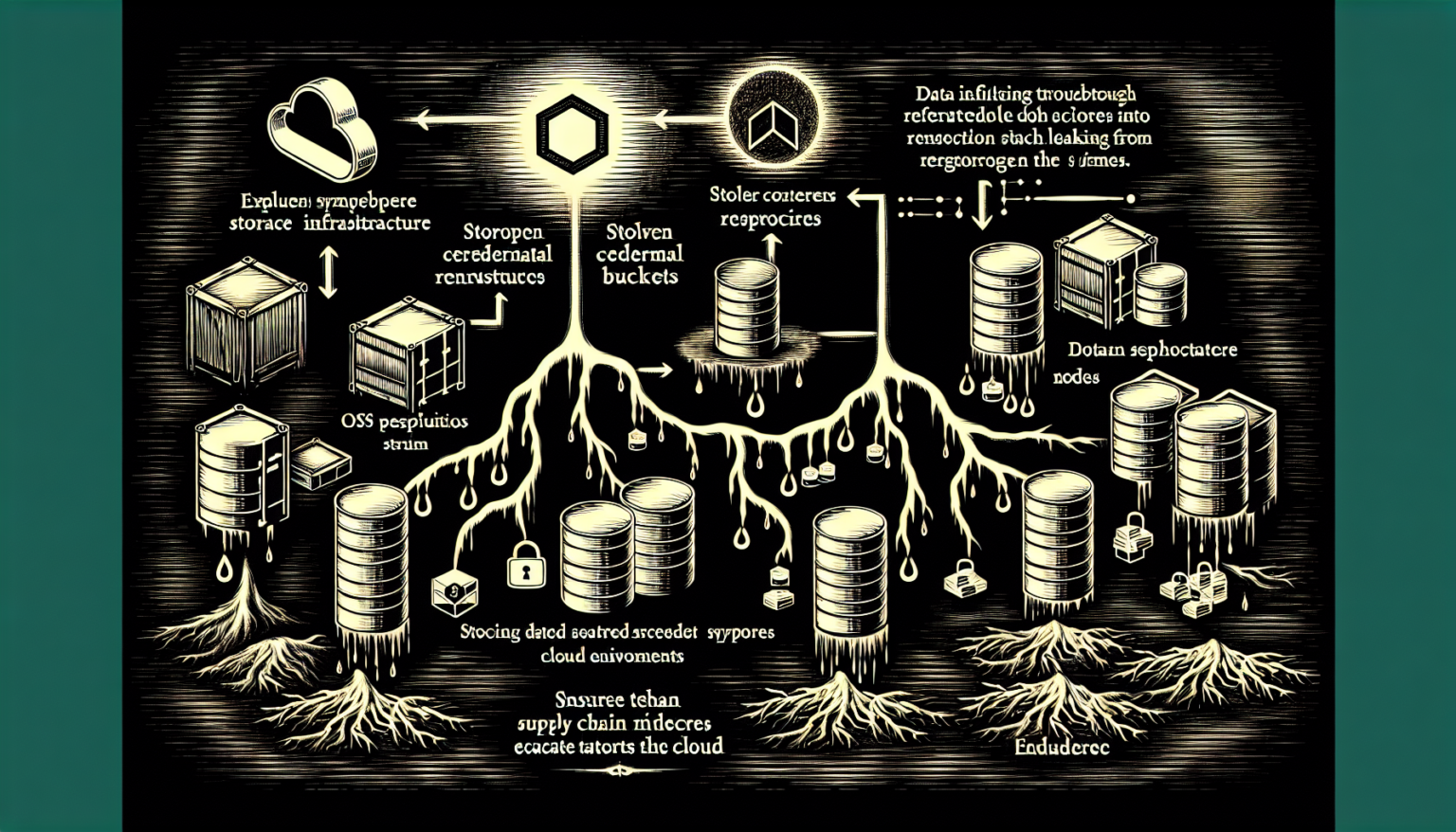
The TeamPCP hacking group used compromised credentials from the Trivy supply chain attack to access AWS environments, enumerate containers, and exfiltrate data from S3 buckets and Secrets Manager.
The threat actor behind the widespread March campaign targeting open source software has been using compromised credentials to access AWS environments and exfiltrate data, according to a new report from Wiz. TeamPCP, also known as DeadCatx3 and ShellForce, made headlines after hacking Aqua Security’s Trivy vulnerability scanner, with the campaign expanding to NPM, PyPI, and OpenVSX, impacting tens of thousands of repositories.
The Trivy hack was the result of improperly rotated credentials following a February compromise. Malware injected into Trivy packages and GitHub Actions was executed when Trivy ran in downstream pipelines, allowing TeamPCP to compromise publish tokens of NPM developers and a PyPI token belonging to LiteLLM co-founder and CEO Krrish Dholakia. LiteLLM, with over 90 million monthly downloads, had its PyPI token exposed, which led to Telnyx packages being injected with malware. The group used the open-source tool TruffleHog to validate stolen AWS access keys, Azure secrets, and SaaS tokens within 24 hours of exfiltration.
Once validated, TeamPCP moved to discovery operations in compromised AWS environments, enumerating containers, mapping clusters and task definitions, and targeting AWS Secrets Managers. The hackers relied on GitHub workflows to execute code within victim environments and used the ECS Exec feature to run Bash commands and Python scripts directly on containers. They accessed S3 buckets, Secrets Manager, and databases for bulk data exfiltration, stealing source code, configuration files, and embedded secrets.
Wiz notes that the exfiltrated data and compromised secrets are potentially being shared with other groups, with suspects including the extortion group Lapsus$ and the VECT ransomware group. TeamPCP’s post-compromise activities focused on compromising additional secrets and exfiltrating massive amounts of data from code repositories and cloud resources, enabling a range of secondary operations by partner threat actors.
Source: SecurityWeek — TeamPCP Moves From OSS to AWS Environments Using Stolen Credentials