CVE-2026-3854 allowed any authenticated user to compromise GitHub backend servers via injected git push options, exposing millions of private repositories.
A critical remote code execution vulnerability tracked as CVE-2026-3854 in GitHub’s internal git infrastructure could have allowed any authenticated user to compromise backend servers, access millions of private repositories, and achieve full server takeover on GitHub Enterprise Server. Discovered by Wiz researchers through AI-augmented reverse engineering of closed-source compiled binaries, this marks one of the first critical vulnerabilities found using AI tooling at scale.
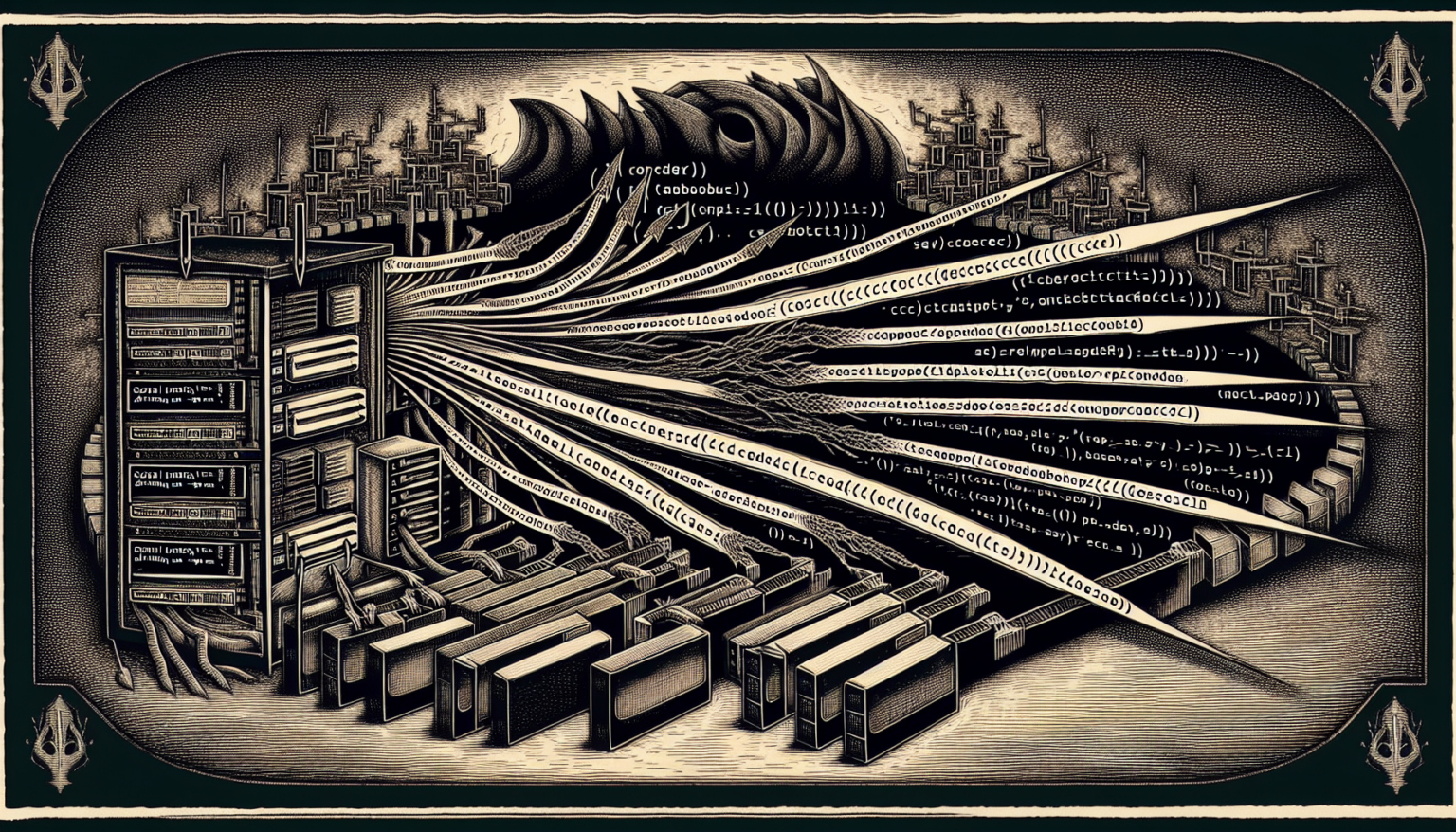
The vulnerability stems from improper neutralization of special elements (CWE-77) in how GitHub’s internal babeld git proxy handled user-supplied push option values. When a user executes git push -o, arbitrary option strings are passed to the server. The proxy copied these values verbatim into a semicolon-delimited internal header without sanitizing the semicolon character. By chaining three injected fields, an attacker could bypass the sandbox execution path, redirect hook directories, and execute arbitrary filesystem binaries. The entire exploit required no privilege escalation, special tooling, or zero-day dependencies — just a standard git client.
On GitHub Enterprise Server, exploitation granted full server compromise including read/write access to all hosted repositories and internal secrets. On GitHub.com, Wiz discovered that an injectable enterprise_mode flag enabled the full chain on shared infrastructure, with the git service user having filesystem access to millions of repositories across tenants. Wiz used IDA MCP for automated reverse engineering, enabling rapid reconstruction of GitHub’s internal protocols across compiled binaries.
GitHub received the report on March 4, 2026, validated it within hours, and deployed a fix by 7:00 p.m. UTC the same day. GHES patches are available for versions up to 3.19.4+. At disclosure, 88% of GHES instances remained unpatched. GHES administrators should audit /var/log/github-audit.log for push operations containing unusual special characters.
Source: Cyber Security News — Critical GitHub.com and Enterprise Server RCE Vulnerability Enables Fu