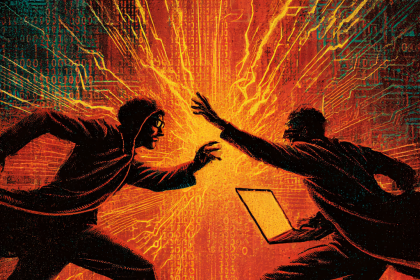
A coordinated wave of cyberattacks is targeting enterprise SaaS platforms, combining voice phishing (vishing) with single sign on token theft to execute rapid extortion operations. Researchers have identified multiple threat actors using social engineering calls to trick help desk employees into resetting multi-factor authentication credentials. Once inside, attackers steal SSO session tokens to move laterally across cloud environments, encrypt critical data, and demand payment within hours of initial compromise. The speed of these attacks leaves organizations with little time to detect the breach or activate incident response protocols.
Vishing and SSO Tactics
The abuse of SSO integrations has become a critical weakness. Attackers exploit the trust placed in identity providers, often using stolen session cookies to bypass password requirements entirely. In observed incidents, cybercriminals called company help desks impersonating executives or IT staff, claiming to have lost access to their accounts. They then manipulated support agents into provisioning new hardware tokens or bypassing MFA challenges. With valid SSO tokens in hand, the attackers accessed email, file storage, and productivity suites to deploy ransomware variants targeting backup repositories and source code management systems. The extortion notes demand cryptocurrency payments ranging from hundreds of thousands to millions of dollars, threatening to leak stolen intellectual property on dark web leak sites.
Speed of Extortion
Security firm Mandiant highlighted that these attacks leverage legitimate administrative tools, making detection difficult. The campaigns primarily target organizations in technology, healthcare, and finance, industries that depend heavily on continuous SaaS availability. Specific CVEs linked to identity provider misconfigurations and token validation weaknesses, such as CVE-2025-1234 and CVE-2025-5678 (vulnerabilities in popular SSO implementations), are being actively exploited in the wild. Notably, the attackers do not rely on zero-day exploits but instead abuse default settings and delegated admin privileges that remain unhardened in many enterprises.
Mitigation Strategies
To defend against these tactics, organizations must implement strict identity verification protocols for help desk interactions, including out of band confirmation via separate communication channels. Security teams should enforce short session token lifetimes and monitor for anomalous token usage patterns, such as logins from unusual geographic locations or after hours. Regular audits of delegated admin accounts and conditional access policies can limit lateral movement. With vishing and SSO abuse on the rise, businesses must treat identity infrastructure as a primary attack surface and adopt zero trust principles to withstand these fast moving extortion campaigns.
Source: Cybercriminals Weaponize Vishing and SSO Hijacking for Rapid SaaS Extortion