Phoneix analysts note that the attackers bypass security filters by piggybacking on the legitimate certificates and domains of Google AppSheet and Netlify.
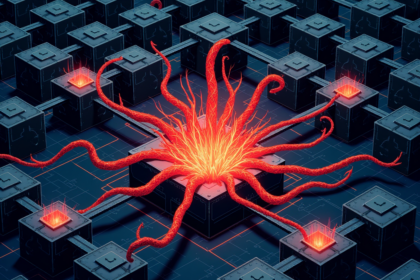
Attack Method and Infrastructure
Researchers have uncovered a sophisticated phishing campaign that exploits trusted cloud platforms to steal Facebook login credentials. The attackers abuse Google AppSheet, Netlify, and Telegram to create convincing fake login pages and manage stolen data. By hosting phishing forms on AppSheet and using Netlify for domain redirection, the campaign bypasses many traditional URL reputation filters that typically block known malicious domains. Telegram bots serve as the command channel, automatically receiving stolen credentials in real time.
Impact and Defensive Guidance
The campaign targets Facebook users globally, relying on the inherent trust users place in legitimate services like appsheet.com and netlify.app. No CVEs are associated since no software vulnerabilities are exploited; the abuse involves misusing platform features. Users should enable two-factor authentication on their Facebook accounts, scrutinize URLs before entering credentials, and avoid clicking links in unsolicited messages. Organizations should consider blocking or monitoring traffic involving these platforms when used in unexpected ways.
Source: Cyber Security News