How the Attack Works
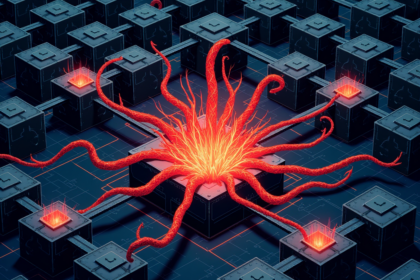
Google’s Threat Analysis Group (TAG) has identified a new generation of cyberattacks where adversaries leverage artificial intelligence to autonomously discover and weaponize zero day vulnerabilities. According to the report, threat actors are using large language models (LLMs) to analyze source code for previously unknown flaws, then generating functional exploit code that can be deployed against unpatched systems. The AI systems are capable of identifying subtle coding errors that traditional static analysis tools might miss, significantly accelerating the timeline from vulnerability discovery to active exploitation.
The process involves feeding LLMs with public code repositories and vulnerability databases to train them on patterns that lead to exploitable conditions. Once a potential zero day is identified, the AI can craft polymorphic shellcode that evades signature based detection systems. Researchers demonstrated that these AI generated exploits can adapt their attack vectors based on the target environment, making them particularly dangerous for organizations relying on traditional security controls.
Impact and Scope
This development represents a paradigm shift in offensive cybersecurity capabilities. Previously, zero day exploits required significant manual effort from skilled human researchers, often taking weeks or months to develop. With AI assistance, attackers can now generate working exploits in hours. Google TAG noted that several advanced persistent threat (APT) groups have already incorporated AI generated exploits into their toolkits, targeting a wide range of software including web servers, database platforms, and enterprise authentication systems. The potential for rapid, large scale exploitation increases dramatically as these techniques become more accessible.
Defenders must adapt their strategies accordingly. Traditional vulnerability management cycles may prove too slow against AI driven attacks that can exploit flaws before patches are even developed. Security teams should prioritize runtime application self protection (RASP) and behavior based detection systems that can identify malicious activities regardless of the specific vulnerability exploited. Google has also called for industry wide collaboration to develop AI driven defensive tools that can match the speed of AI powered attackers.
Source: Cyber Security News