Claroty discovered critical security bypass and RCE flaws (CVE-2026-22885, CVE-2026-20761) in EnOcean’s SmartServer IoT gateway, enabling full takeover of building management systems.
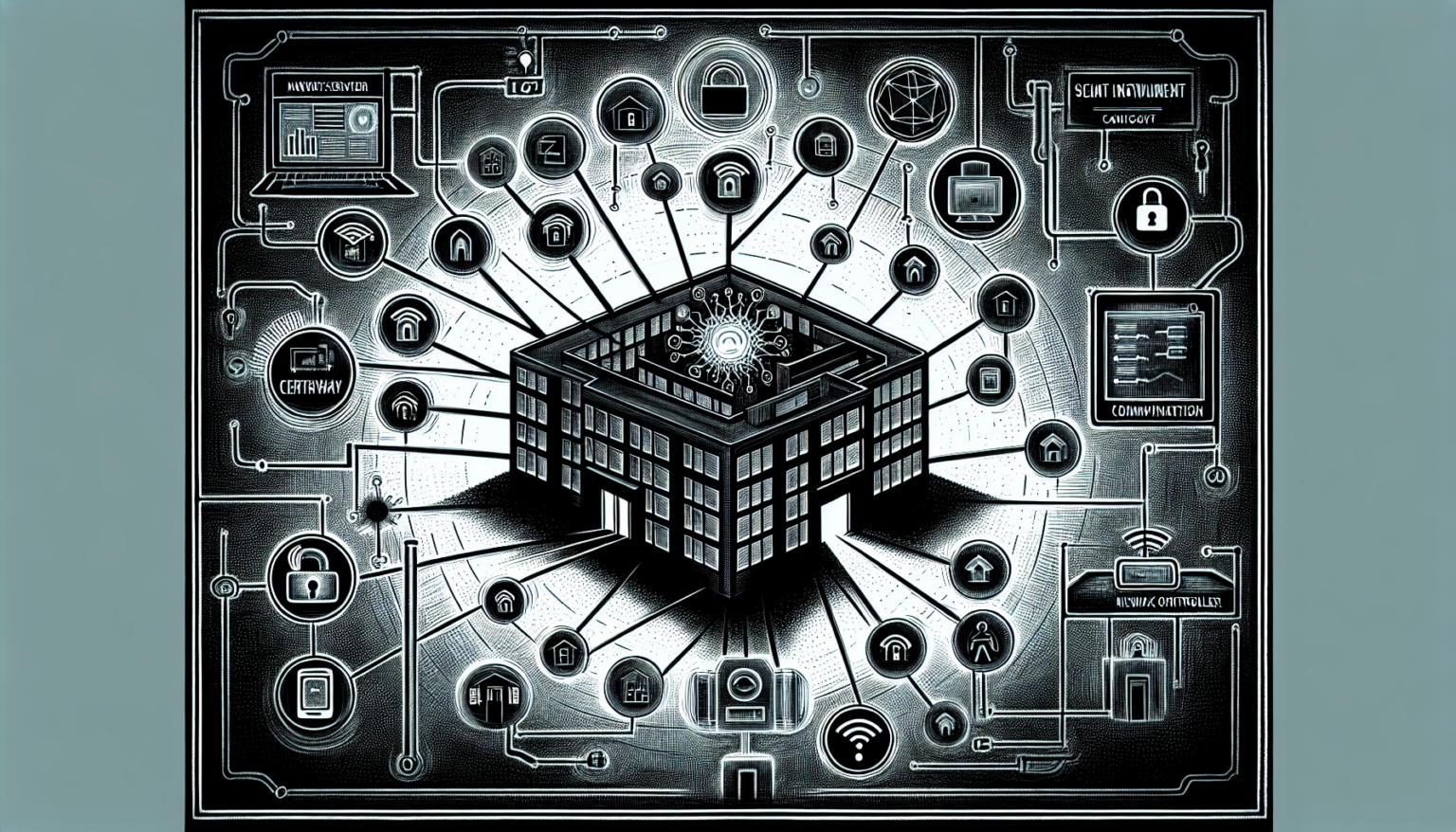
Vulnerabilities discovered by Claroty researchers in EnOcean’s SmartServer IoT platform can be exploited to remotely hack building management systems. EnOcean SmartServer is a multi-protocol gateway and edge controller designed to unify building automation by connecting industrial devices to cloud-based management platforms, marketed for smart buildings, factories, and data centers.
Two critical vulnerabilities were identified: CVE-2026-22885, a security bypass flaw, and CVE-2026-20761, a remote code execution vulnerability. By exploiting improper validation of packet input, an attacker can control an argument passed to the device’s built-in system call and achieve full takeover of the Linux-based device, gaining root privileges and arbitrary code execution. The vulnerabilities can be exploited by remote attackers against internet-exposed EnOcean devices to bypass memory protections, leak memory, and execute arbitrary commands.
In a real-world environment, threat actors could take control of building management and automation systems, affecting HVAC, lighting, access control, and other critical building functions. The security holes also impact legacy i.LON devices in addition to the SmartServer line.
EnOcean has released SmartServer 4.6 update 2 (4.60.023) to patch these vulnerabilities. Claroty has published technical details and proof-of-concept exploits. Organizations using EnOcean SmartServer or legacy i.LON devices should update immediately and review whether their devices are exposed to the internet.
Source: SecurityWeek — EnOcean SmartServer Flaws Expose Buildings to Remote Hacking