Overview
A sophisticated, high-resilience malware campaign dubbed EtherRAT was identified by Atos Threat Research Center (TRC) in March 2026. This operation specifically targets high-privilege enterprise accounts (administrators, DevOps engineers, and security analysts) by impersonating the administrative utilities they rely on daily. The campaign integrates SEO poisoning, a dual-stage GitHub distribution architecture, and decentralized blockchain-based command-and-control (C2) via Ethereum smart contracts, creating one of the technically most mature malware distribution chains observed in recent months.
Distribution via GitHub Facades
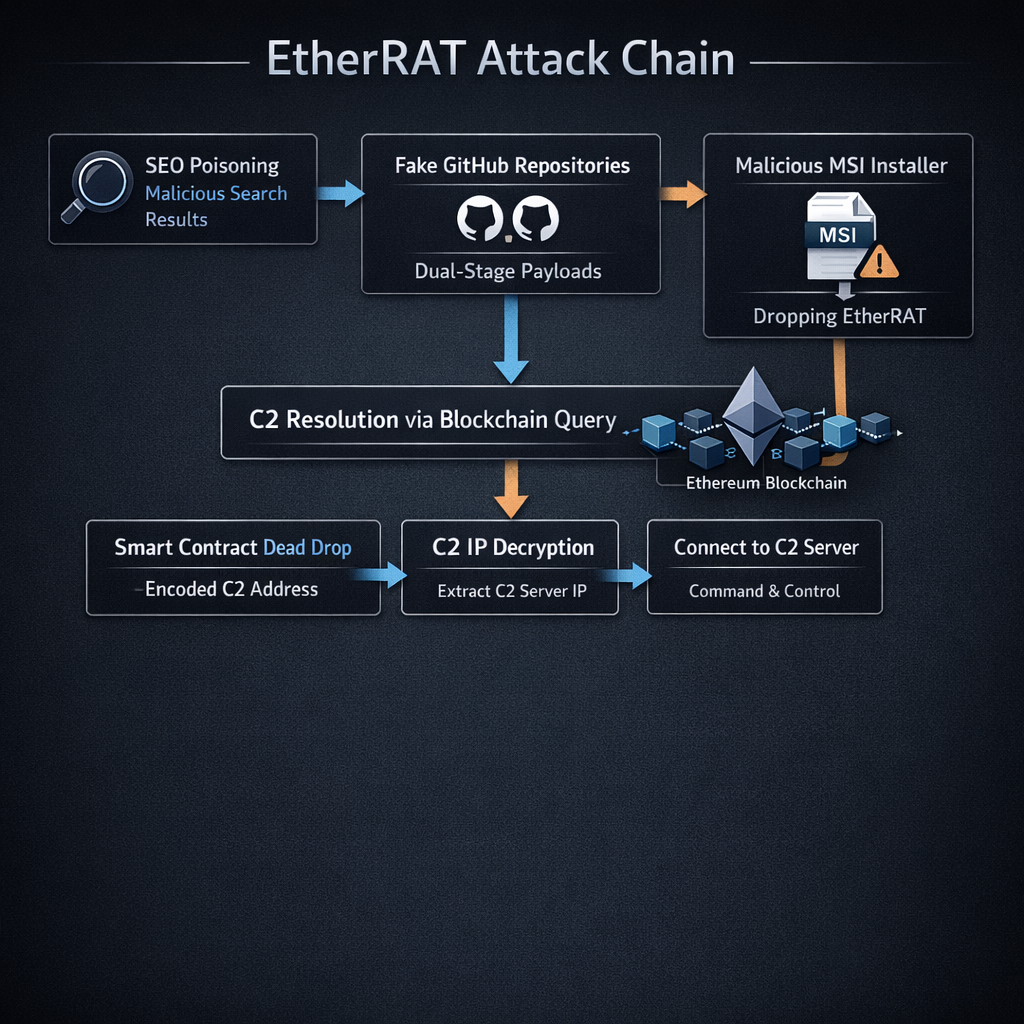
The attack begins with SEO poisoning across multiple search engines including Bing, Yahoo, DuckDuckGo, and Yandex. Threat actors ensure that malicious links for niche IT terms rank at the top of search results. Users searching for tools like Kusto Explorer, ProcDump, or LAPS are directed to a primary “facade” GitHub repository: a clean, professional-looking storefront with no malicious code.
This facade repo contains a link in its README pointing to a second, hidden GitHub repository that hosts the actual malware payload. By separating the SEO-optimized storefront from the payload delivery account, the threat actors can rapidly rotate distribution repositories if flagged, while the search-indexed facade remains untouched. Between early December 2025 and April 1, 2026, the actors deployed 44 separate GitHub facades, each spoofing a different administrative tool.
Strategic Tool Impersonation
The campaign is characterized by its focus on the enterprise administrative stack. Malicious MSI installers disguise themselves as:
- Sysinternals/Diagnostics: Autoruns, ProcDump, RAMMap, TCPView, Process Monitor, Process Explorer, Disk2vhd, Sysmon, DebugView, WinDbg, BgInfo
- AD/Credential/Admin: Windows ADK, Windows LAPS, RSAT, IIS Crypto, Profwiz, PCmover, Transwiz, Delprof2
- Remote Access: Dameware, SecureCRT, SuperPuTTY, ScreenConnect Client, Bitvise SSH Client, TeraTerm
- Data Transfer/Cloud: AzCopy, FSLogix
- Security/Auth: AppLocker, SafeNet Authentication Client, NSSM
- Network/Debugging: PRTG Network Monitor, HTTP Debugger
- Utility/Business Apps: KDiff3, Beyond Compare, BarTender, PaperPort
- Misc Sysadmin Tools: Autologon, Kusto Explorer, LEAP Desktop, VMware Tools
These tools are almost exclusively used by personnel with elevated network and system permissions. A successful infection on an administrator’s workstation can provide the “keys to the kingdom,” facilitating lateral movement inside the enterprise environment.
Blockchain-Based Command and Control
The most technically significant aspect of EtherRAT is its implementation of Blockchain-based Dead Drop Resolving (DDR). Once the malicious MSI is executed, the malware does not reach out to a hardcoded domain or IP address that could be easily blocklisted. Instead, it repetitively queries a public Ethereum (ETH) RPC endpoint.
The malware is hardcoded with a specific smart contract address on the Ethereum blockchain. By querying this contract, it dynamically retrieves the live C2 server address. This technique provides extreme resilience:
- Infrastructure agility: Attackers can rotate C2 servers globally simply by updating the value stored in the blockchain contract
- Robustness: As long as public Ethereum gateways are accessible, the malware can always find its home, making traditional domain takedowns or IP blocks ineffective
This approach (sometimes called “EtherHiding”) represents a significant evolution in C2 infrastructure design, leveraging the decentralized and immutable nature of blockchain technology to create a takedown-resistant communication channel.
Victimology and Attribution
The campaign is notable for its surgical targeting of enterprise environments. Unlike broad-spectrum malware campaigns that cast a wide net across general consumers, EtherRAT is focused on the “crown jewel” accounts of the enterprise: those with privileged access to critical systems and data.
Security researchers including Sysdig have noted overlaps with North Korean APT group tactics, techniques, and procedures (TTPs), particularly the “Contagious Interview” social engineering playbook. However, definitive attribution remains challenging, as the campaign’s infrastructure and tooling could be adopted by multiple threat actors.
Mitigation and Defense
Organizations can protect themselves by implementing the following measures:
- Employee training: Educate staff to recognize and report suspicious search results for common administrative tools
- Application control: Disable unnecessary Windows utilities and implement strict software installation policies
- Network monitoring: Monitor for connections to public Ethereum RPC endpoints from non-cryptocurrency workstations
- EDR solutions: Apply recommended policies for endpoint detection and response, including delayed execution for cloud scans
- Patch management: Promptly patch critical vulnerabilities such as CVE-2025-55182 (React2Shell) that have been used in conjunction with EtherRAT deployment
- GitHub hygiene: Verify the authenticity of GitHub repositories before downloading administrative tools: check repository age, commit history, and publisher identity
Conclusion
The EtherRAT campaign represents a significant maturation of sophisticated malware delivery techniques. By combining SEO poisoning, dual-stage GitHub distribution, and blockchain-based C2 infrastructure, the threat actors have created a resilient and difficult-to-disrupt attack chain. The campaign’s focus on enterprise administrative tools makes it a particularly dangerous threat to organizations of all sizes.
Atos TRC’s research provides a comprehensive technical analysis based on long-term observation and active detonation within a controlled environment. Their findings confirm that the malware continues to evolve, with several distinct variants and additional C2 infrastructure identified since the campaign’s inception.
For the full technical deep dive, refer to the original research sources linked below.
Source: The Hacker News — EtherRAT Distribution Spoofing Administrative Tools via GitHub Facades