Overview
Security researchers at Securonix have uncovered a stealthy Python-based backdoor framework dubbed DEEP#DOOR that establishes persistent access on compromised systems and harvests a wide range of sensitive information, including browser credentials, SSH keys, and cloud provider tokens. What sets this malware apart is its innovative use of a public TCP tunneling service for command-and-control communications, eliminating the need for dedicated attacker infrastructure.
Infection Chain
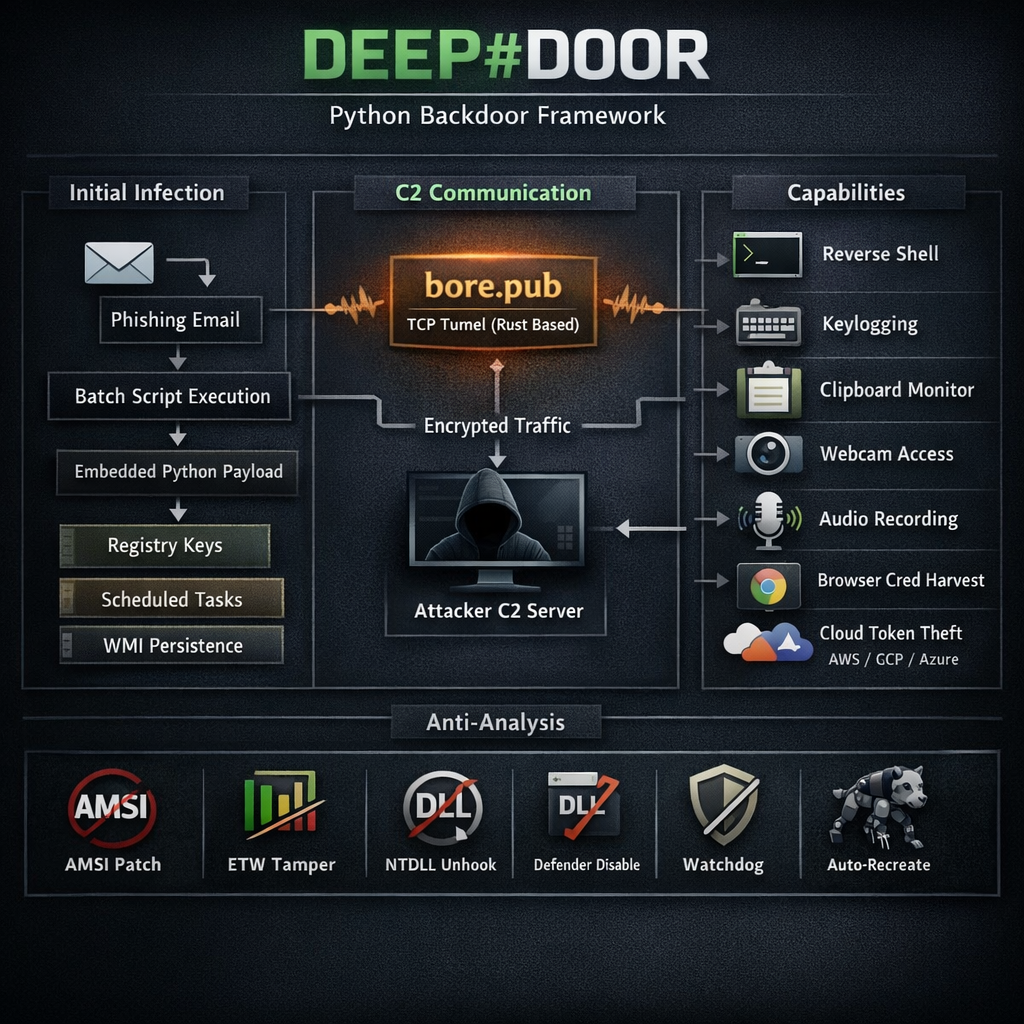
The intrusion chain begins with the execution of a batch script (install_obf.bat) that disables Windows security controls, dynamically extracts an embedded Python payload (svc.py), and establishes persistence through multiple mechanisms, including Startup folder scripts, registry Run keys, scheduled tasks, and optional WMI subscriptions. The initial infection vector is assessed to be traditional phishing campaigns.
A distinctive aspect of the attack chain is that the core Python implant is embedded directly inside the dropper script. It is extracted, reconstructed, and executed at runtime, reducing the need for repeated network callouts and minimizing the forensic footprint. This fileless approach makes detection significantly more challenging for traditional antivirus solutions.
Command and Control
Once operational, the malware establishes communication with bore[.]pub, a Rust-based public TCP tunneling service. This approach offers several advantages to the attackers:
- No dedicated infrastructure needed: The tunneling service handles traffic routing, eliminating setup costs and server management
- Traffic blending: Malicious communications blend in with legitimate bore.pub traffic, evading network-based detection
- Payload resilience: No hardcoded C2 server details are embedded, so the payload remains viable even if a specific endpoint is discovered
Through this tunneling channel, the operator can issue commands enabling a wide range of surveillance and control capabilities.
Capabilities
DEEP#DOOR functions as a fully featured Remote Access Trojan (RAT) with extensive espionage and surveillance features:
- Reverse shell for interactive command execution
- System reconnaissance to map the compromised environment
- Keylogging and clipboard monitoring to capture typed credentials and copied data
- Screenshot capture and webcam access for visual surveillance
- Ambient audio recording through connected microphones
- Web browser credential harvesting from Chrome, Firefox, and Windows Credential Manager
- SSH key extraction for lateral movement across managed systems
- Cloud credential theft targeting AWS, Google Cloud, and Microsoft Azure
Anti-Analysis and Evasion
The malware incorporates a comprehensive suite of defense evasion mechanisms that make it particularly difficult to detect and remediate:
- Sandbox, debugger, and VM detection to avoid analysis environments
- AMSI patching to bypass PowerShell script detection
- Event Tracing for Windows (ETW) tampering to blind security monitoring
- NTDLL unhooking to evade userland API hooks from EDR solutions
- Microsoft Defender tampering and SmartScreen bypass
- PowerShell logging suppression, command-line wiping, timestamp stomping, and log clearing
A particularly challenging feature is the watchdog mechanism. The malware actively monitors its persistence artifacts and automatically recreates any that are removed, making manual cleanup difficult and requiring comprehensive removal procedures.
Attribution and Threat Profile
Based on Securonix’s analysis, there is no clear evidence that this malware framework was used in large-scale or highly active campaigns. Its observed usage appears to be limited and somewhat targeted rather than broadly distributed. However, given the modular nature of the framework, different threat actors could adapt it for varied use cases over time. No consistent indicators pointing to specific geographies or industry sectors being systematically targeted have been identified.
As Securonix noted: “DEEP#DOOR highlights the continued evolution of threat actors toward fileless, script-driven intrusion frameworks that rely heavily on native system components and interpreted languages like Python.”












