Overview
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has ordered federal agencies to patch a critical Windows vulnerability, tracked as CVE-2026-32202, that has been exploited in zero-day attacks. The vulnerability (a zero-click NTLM hash leak) poses significant risks to enterprise environments and has been linked to the Russian state-sponsored group APT28 (Fancy Bear).
Technical Details
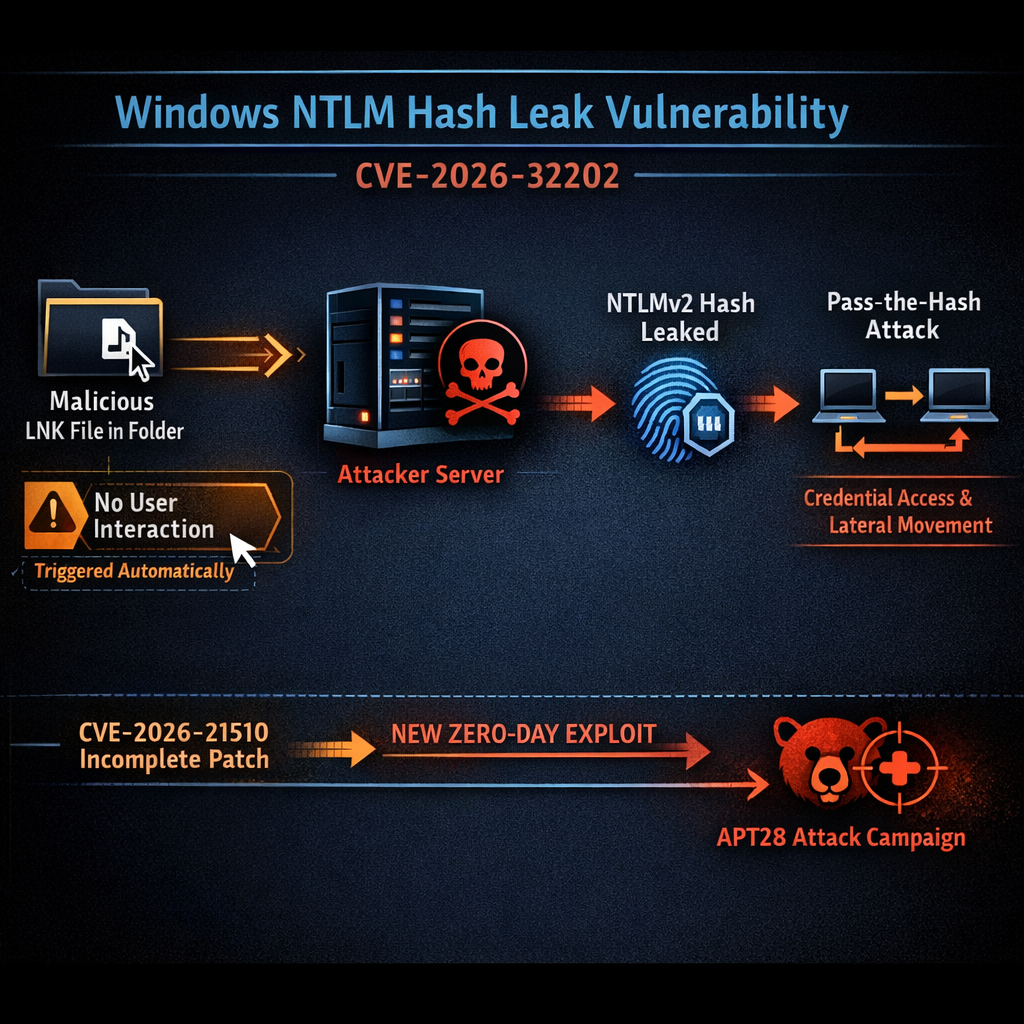
CVE-2026-32202 is described as a protection mechanism failure within the Microsoft Windows Shell. The flaw originated from an incomplete patch issued in February 2026 for CVE-2026-21510, a remote code execution vulnerability previously exploited by APT28 in attacks against Ukraine and European Union countries in December 2025. While Microsoft has stated they haven’t found direct evidence linking APT28 to exploitation of CVE-2026-32202 itself, cybersecurity firm Akamai (which discovered the incomplete patch) did link the initial APT28 exploit to the chain that created this new vulnerability.
The vulnerability can be leveraged in pass-the-hash attacks. This allows adversaries to steal NTLM hashes from vulnerable Windows systems without any user interaction: simply browsing a folder containing a malicious LNK file is sufficient. The incomplete patch failed to prevent Windows from initiating a Server Message Block (SMB) connection to an attacker’s server when rendering the contents of such a folder. This SMB connection automatically triggers an NTLM authentication handshake, sending the victim’s NTLMv2 hash to the attacker.
Once stolen, these NTLMv2 hashes can be used for NTLM relay attacks or offline cracking to authenticate as the compromised user, facilitating lateral movement across networks and data theft, all without the attacker needing to know the actual password.
APT28 Background
APT28 (also tracked as Fancy Bear, Strontium, and Sofacy) is a Russian military intelligence unit (GRU) that has been linked to numerous high-profile cyber operations, including the 2016 Democratic National Committee (DNC) hack and ongoing campaigns against government, military, and critical infrastructure targets worldwide. The group is known for sophisticated cyber espionage operations and has been increasingly active in targeting Ukrainian infrastructure and European allies.
CISA Directive and Timeline
CISA has added the vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog and mandated that all U.S. federal agencies apply the latest security updates by May 12, 2026 under Binding Operational Directive (BOD) 22-01. The exploitation of CVE-2026-21510 was first observed in late 2025. The incomplete patch led to the emergence of CVE-2026-32202, which attackers have now exploited in active campaigns.
Recommendations
System administrators are urged to:
- Apply the latest Windows security updates from Microsoft’s April 2026 Patch Tuesday
- Monitor for NTLM authentication anomalies and unexpected SMB connections in network logs
- Implement NTLM blocking where possible, moving toward Kerberos-only authentication
- Restrict SMB outbound connections at network boundaries to limit pass-the-hash attack paths
Organizations outside the federal government are also strongly advised to prioritize this patch given the active exploitation and the severity of potential pass-the-hash lateral movement within enterprise networks.
Source: BleepingComputer: CISA Orders Federal Agencies to Patch Windows Zero-Day Exploited by Russian APT28