Overview
A newly disclosed Linux kernel vulnerability, tracked as CVE-2026-31431 and dubbed “Copy Fail,” allows an unprivileged local attacker to escalate privileges to root on major Linux distributions within seconds. A public exploit (a compact 732-byte Python script) has already been released, and the flaw has been present in the kernel since 2017.
Technical Details
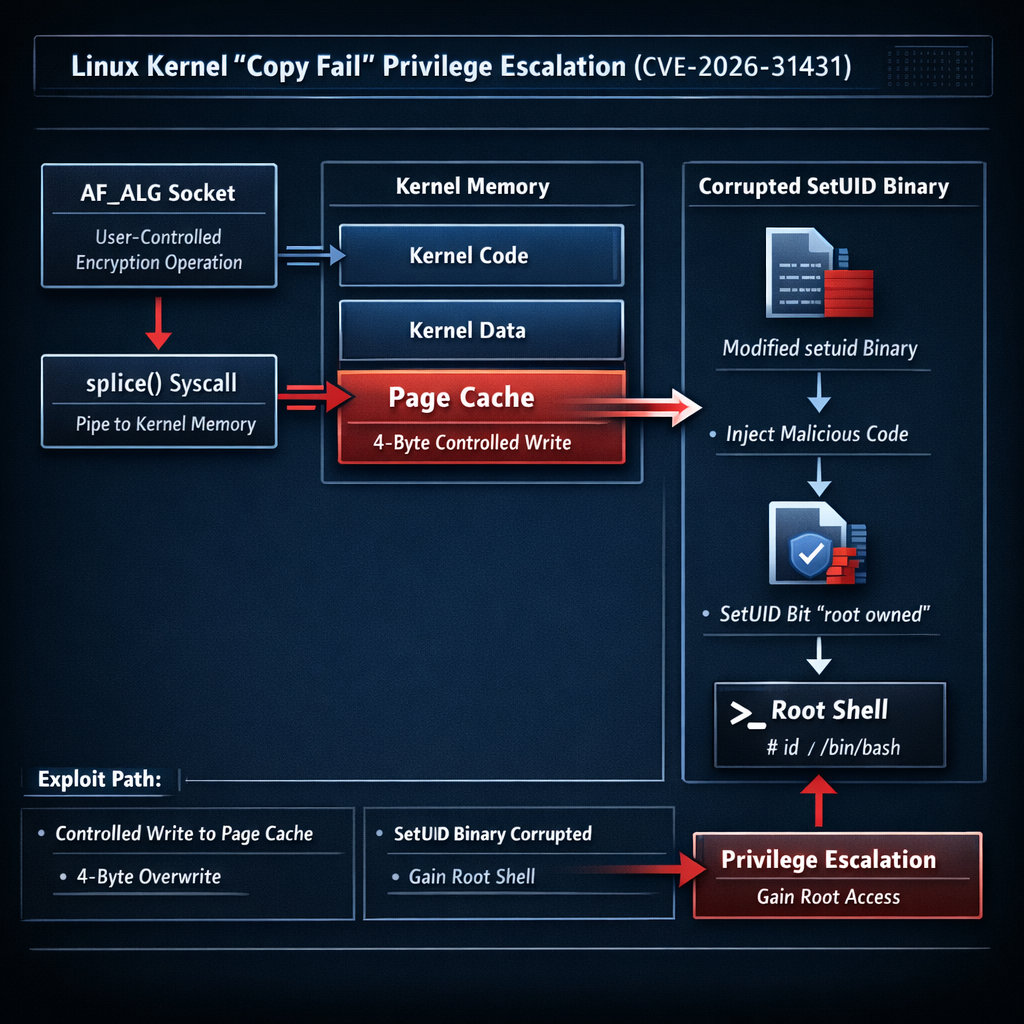
The vulnerability resides in the Linux kernel’s algif_aead userspace crypto interface: specifically the AEAD socket interface of the kernel’s userspace crypto API (AF_ALG). The flaw was introduced in 2017 via commit 72548b093ee3, which switched AEAD operations to in-place processing. This optimization inadvertently allowed page-cache pages to be placed into a writable destination scatterlist.
By chaining an AF_ALG socket operation with splice(), an unprivileged local user can perform a controlled 4-byte write to an arbitrary page-cache-backed page. This can be used to corrupt the page cache backing setuid binaries, such as /usr/bin/su, to obtain a root shell. The exploit is highly reliable, requiring no race conditions, timing windows, or version-specific payloads, making it particularly dangerous for enterprise environments.
Impact and Affected Systems
The vulnerability carries a CVSS score of 7.8 and affects every mainstream Linux distribution shipping a kernel built since 2017. Verified affected distributions include:
- Ubuntu 24.04
- Amazon Linux 2023
- Red Hat Enterprise Linux (RHEL) 10.1 and 14.3
- SUSE 16 kernels
The flaw is particularly dangerous in containerized environments. Since the page cache is shared across containers and the host, a compromised container can escape to the host, posing a significant threat to multi-tenant container platforms, Kubernetes clusters, and CI/CD runners.
Detection Evasion
A concerning aspect of Copy Fail is that exploitation modifies data in the page cache in memory, not on disk. This means standard file integrity checks (such as those performed by file scanning or integrity monitoring tools) may not detect the tampering, as the changes exist only in memory and are never written back to the filesystem.
Patches and Mitigation
The mainline fix was committed on April 1, 2026, reverting the 2017 optimization (commit a664bf3d603d). System administrators should prioritize the following actions:
- Update kernels to versions 7.0, 6.19.12, or 6.18.22 (or corresponding distribution backports for older LTS lines)
- Restrict AF_ALG socket creation via seccomp profiles, container runtime defaults, or by disabling
CONFIG_CRYPTO_USER_API_AEAD - Kubernetes users: Apply immediate runtime restrictions on AF_ALG syscall access to prevent container escape
Major distribution vendors have already begun rolling out kernel updates addressing the issue. Given the broad impact window spanning nearly a decade and the availability of a public exploit, system administrators are urged to prioritize patching as a critical security action.
Background
This follows a broader wave of critical vulnerabilities being actively exploited against Linux systems, as threat actors increasingly target the open-source kernel with privilege escalation techniques. The Copy Fail bug is considered particularly dangerous due to its long shelf life, the ease with which the public exploit can be weaponized, and its implications for containerized environments.
Source: BleepingComputer: New Linux ‘Copy Fail’ Flaw Gives Attackers Root Access on Major Distributions