Overview
The open-source PyTorch Lightning Python framework was hit by a supply chain attack on April 30, 2026, with threat actors pushing two malicious versions (2.6.2 and 2.6.3) to the PyPI repository. The malicious packages were designed to steal credentials from developers and propagate through their environments, marking one of the most sophisticated Python supply chain attacks observed to date.
Technical Breakdown
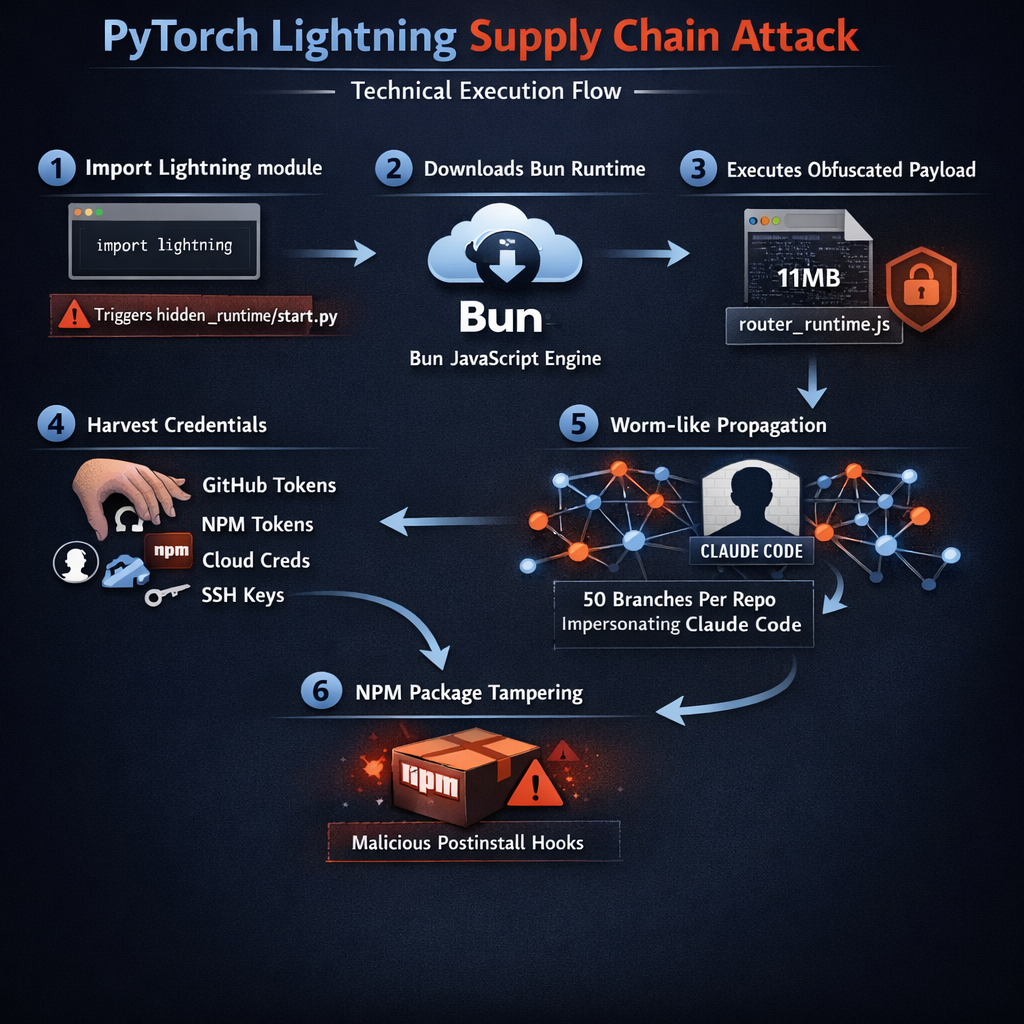
According to multiple security firms tracking the incident (including Aikido Security, OX Security, Socket, and StepSecurity) the malicious packages include a hidden _runtime directory containing a downloader and an obfuscated JavaScript payload. Socket noted that “the execution chain runs automatically when the lightning module is imported, requiring no additional user action after installation and import.”
The attack chain unfolds in several stages:
- Stage 1: A Python script (start.py) executes upon module import
- Stage 2: The script downloads and executes the Bun JavaScript runtime
- Stage 3: Bun runs an 11MB obfuscated payload (router_runtime.js) designed for comprehensive credential theft
Once activated, the malware harvests GitHub tokens, npm tokens, SSH keys, cloud credentials (AWS, GCP, Azure), Kubernetes configurations, Vault secrets, Docker credentials, and .env files. The harvested GitHub tokens are validated against GitHub’s API before being used to inject worm-like payloads into up to 50 branches per accessible repository.
Self-Propagation Mechanism
The attack implements two sophisticated propagation vectors:
GitHub worm: Stolen GitHub tokens are used to inject malicious code into up to 50 branches per repository the token can write to. Each poisoned commit is authored using a hardcoded identity designed to impersonate Anthropic’s Claude Code, making the tampered code appear legitimate.
npm propagation: The malware modifies the developer’s local npm packages by adding a malicious postinstall hook in package.json, incrementing the patch version, and repacking the .tgz tarballs. If the developer publishes these tampered packages, the malware spreads to downstream users on the npm registry, creating a cascading supply chain infection.
Exfiltration Methods
Stolen credentials are encrypted and exfiltrated to a remote server at zero.masscan[.]cloud:443/v1/telemetry. If this primary channel is blocked, the malware falls back to a GitHub-based exfiltration method, using the pilfered tokens to create a public repository with the description “A Mini Shai-Hulud has Appeared” containing the stolen data.
Remediation Status
The PyPI quarantine on the Lightning package has been lifted and the malicious versions have been deleted. The last known clean version is 2.6.1. PyTorch Lightning maintainers have acknowledged the incident and are actively investigating, with indications that the project’s GitHub account was compromised. Users are advised to:
- Downgrade to Lightning version 2.6.1 immediately
- Rotate all credentials that may have been exposed in affected environments
- Audit GitHub repositories for unauthorized commits, particularly those authored by “Claude Code” identities
- Review local npm packages for tampered postinstall hooks
Threat Actor Context
The attack is attributed to TeamPCP, the same threat actor behind the Mini Shai-Hulud campaign that targeted SAP-related npm packages earlier in the week. The Intercom npm and Packagist PHP packages were also compromised as part of the same campaign, demonstrating a coordinated multi-ecosystem supply chain operation. TeamPCP has since launched an onion website on the dark web after its X account was suspended, and has claimed partnership with the LAPSUS$ group.
This incident underscores the escalating threat of supply chain attacks targeting the Python and JavaScript ecosystems, where a single compromised package can cascade across hundreds of downstream projects and organizations.
Source: The Hacker News: PyTorch Lightning Supply Chain Attack